
A SQL Injection vulnerability has been discovered in one of the most popular WordPress plugins, installed on over 300,000 websites, which could be exploited by hackers to steal databases and possibly hijack the affected sites remotely.
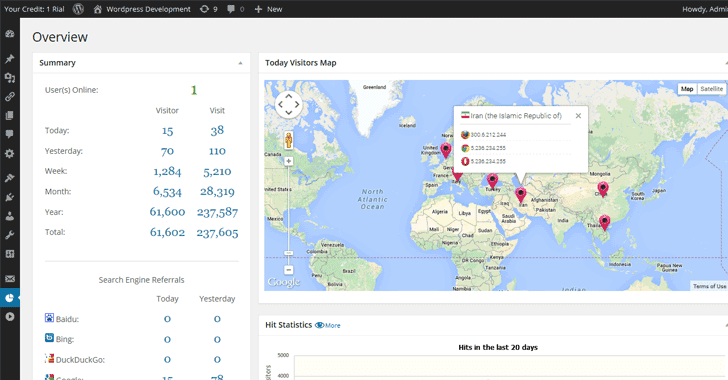
The flaw has been discovered in the highly popular WP Statistics plugin, which allows site administrators to get detailed information related to the number of users online on their sites, the number of visits and visitors, and page statistics.
Discovered by Sucuri team, WordPress plugin WP Statistics is vulnerable to SQL Injection flaw that allows a remote attacker, with at least a subscriber account, to steal sensitive information from the website’s database and possibly gain unauthorized access to websites.
SQL Injection is a web application bug that allows hackers to inject malicious Structured Query Language (SQL) code to web inputs in order to determine the structure and location of key databases, which eventually allows stealing of the database.
The SQL injection vulnerability in WP Statistics plugin resides in multiple functions, including wp_statistics_searchengine_query().
“This vulnerability is caused by the lack of sanitization in user-provided data,” researchers said. “Some attributes of the shortcode wpstatistics are being passed as parameters for important functions and this should not be a problem if those parameters were sanitized.”
“One of the vulnerable functions wp_statistics_searchengine_query() in the file ‘includes/functions/functions.php’ is accessible through WordPress’ AJAX functionality thanks to the core function wp_ajax_parse_media_shortcode().”
This function does not check for additional privileges, which allows website subscribers to execute this shortcode and inject malicious code to its attributes.
The researchers at Sucuri privately disclosed the flaw to the WP Statistics team and the team had patched the vulnerability in its latest version WP Statistics version 12.0.8.
So, if you have a vulnerable version of the plugin installed and your website allowing user registration, you are definitely at risk, and you should install the latest version as soon as possible.


Leave a Reply